Stop Building.Start Deploying.
The AWS European Sovereign Cloud (ESC) just launched and the Nuvibit Terraform Collection (NTC) ESC Blueprint is ready to deploy now.
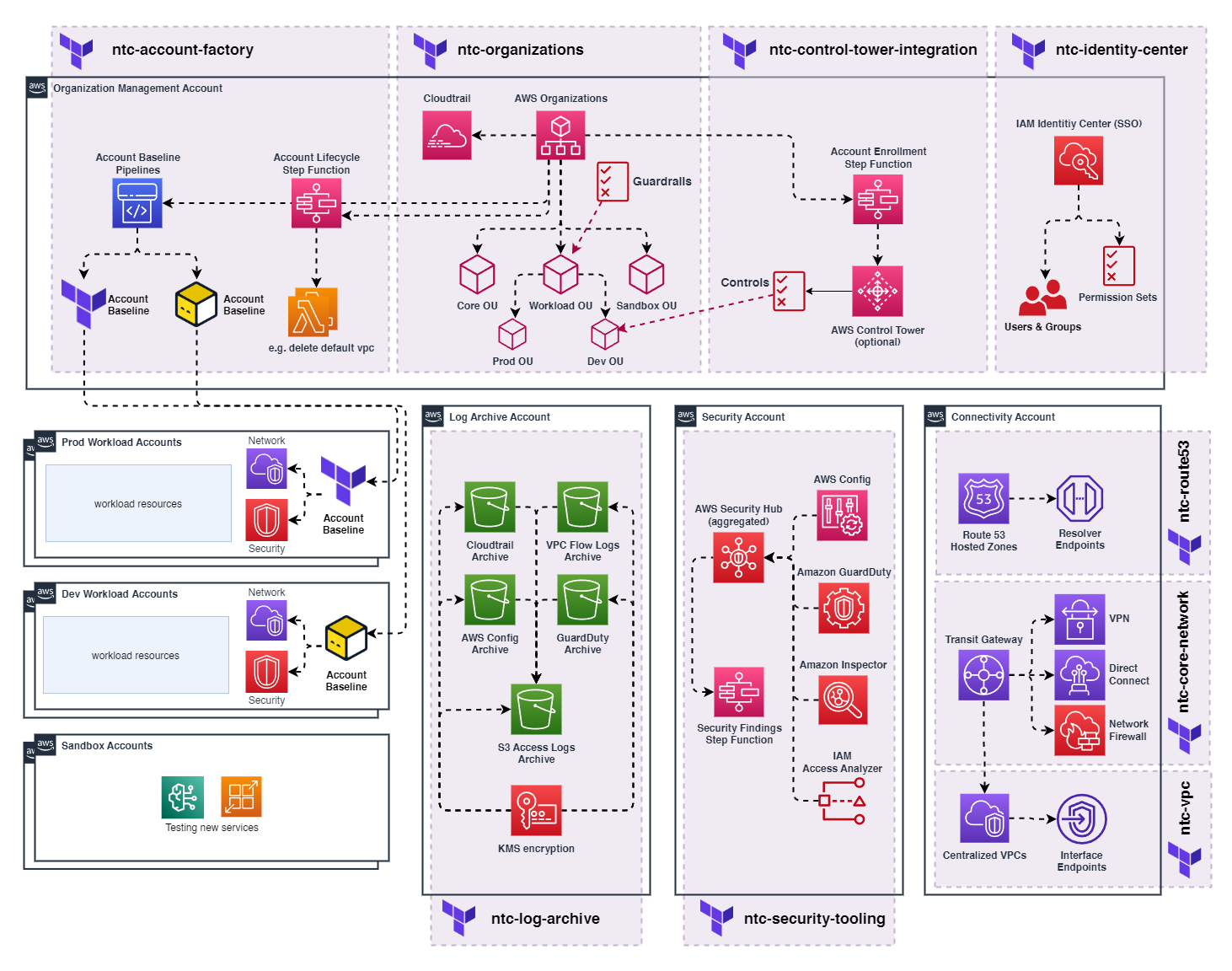
Click image to zoom
Skip 6-12 months of engineering and deploy a production-ready, secure, and compliant landing zone for AWS ESC in weeks, not months.
- ✗Build everything from scratch
- ✗Dedicated cloud architecture team
- ✗Trial-and-error configurations
- ✗Compliance validation delays
- ✓Pre-built landing zone modules
- ✓Security & compliance built-in
- ✓Enterprise-grade
- ✓Ready to deploy apps immediately
AWS ESC Just Launched.We Did the Heavy Lifting.
The AWS European Sovereign Cloud (ESC) is a completely new AWS partition. Every organization must start from scratch: new accounts, new infrastructure, new everything.
Start From Scratch
ESC is a completely new AWS partition. You can't migrate existing AWS accounts or infrastructure. Every organization starts at zero.
Navigate Limitations
ESC has evolving service parity. Not all AWS services are available yet, and some features differ. Understanding these constraints is critical for success.
6-12 Month Timeline
Building a production-ready, secure, and compliant multi-account landing zone requires specialized expertise and massive engineering effort.
Save Months of Trial and Error
As an AWS ESC launch partner, Nuvibit has already built, tested, and deployed a complete multi-account landing zone in the ESC. We know what works and where the pitfalls are.
Instead of spending months figuring it out yourself, deploy our production-ready ESC blueprint and go live in weeks.

The NTC ESC Blueprint
Enterprise-grade multi-account landing zone built specifically for the AWS European Sovereign Cloud
The Blueprint in Action
You're experiencing NTC right now. This website is powered by the NTC ESC blueprint and is hosted entirely in the AWS European Sovereign Cloud:
Production-Ready Building Blocks
Each module is independently versioned, thoroughly tested, and designed to work together seamlessly
Organizations
Multi-account OU structure with SCPs and foundational guardrails
Account Factory
Automated account provisioning with customizable security baselines
Identity Center
Centralized SSO and identity management with fine-grained access controls
Log Archive
Centralized audit logs including CloudTrail, GuardDuty, and Network Flow Logs
Security Tooling
Centralized Security Hub, Config, GuardDuty and IAM Access Analyzer
Route53
DNS management with hosted zones and cross-account configurations
Core Network
Transit Gateway, VPN, and Direct Connect for hybrid connectivity
IPAM
Centralized IP address management preventing CIDR overlaps
VPC
Secure VPCs with subnets, route tables, and network configurations
Everything In Code
100% Infrastructure as Code with compliance built in. Every resource, every configuration, every security control is versioned and auditable. You are in full control.
1# ---------------------------------------------------------------------------------------------------------------------
2# ¦ PROVIDER
3# ---------------------------------------------------------------------------------------------------------------------
4provider "aws" {
5 region = "eusc-de-east-1" # Brandenburg
6}
7
8# ---------------------------------------------------------------------------------------------------------------------
9# ¦ NTC ORGANIZATIONS
10# ---------------------------------------------------------------------------------------------------------------------
11module "ntc_organizations" {
12 source = "github.com/nuvibit-terraform-collection/terraform-aws-ntc-organizations?ref=2.0.0"
13
14 # -------------------------------------------------------------------------------------------------------------------
15 # AWS SERVICE INTEGRATIONS WITH ORGANIZATIONS
16 # -------------------------------------------------------------------------------------------------------------------
17 # Enable trusted access for AWS services to perform actions across your organization
18 #
19 # WHAT THIS DOES:
20 # - Allows services to create service-linked roles in member accounts
21 # - Enables centralized management from the management account
22 # - Required for organization-wide features like GuardDuty, Security Hub, etc.
23 #
24 # SECURITY NOTE: Only enable services you actually use to minimize attack surface
25 #
26 # Reference: https://docs.aws.amazon.com/organizations/latest/userguide/orgs_integrate_services_list.html
27 # -------------------------------------------------------------------------------------------------------------------
28 service_access_principals = [
29 "iam.amazonaws.com", # IAM - Identity and Access Management
30 "account.amazonaws.com", # AWS Account Management
31 "cloudtrail.amazonaws.com", # CloudTrail - Organization-wide audit logging
32 "config.amazonaws.com", # AWS Config - Compliance and configuration tracking
33 "config-multiaccountsetup.amazonaws.com", # AWS Config - Multi-account setup
34 "access-analyzer.amazonaws.com", # IAM Access Analyzer - Identify unintended access
35 "ipam.amazonaws.com", # IPAM - IP address management
36 "securityhub.amazonaws.com", # Security Hub - Centralized security findings
37 "guardduty.amazonaws.com", # GuardDuty - Threat detection
38 "malware-protection.guardduty.amazonaws.com", # GuardDuty Malware Protection
39 "ram.amazonaws.com", # AWS Resource Access Manager - Resource sharing
40 "member.org.stacksets.cloudformation.amazonaws.com" # CloudFormation StackSets - Cross-account deployments
41 ]
42
43 # -----------------------------------------------------------------------------------------------------------------
44 # ORGANIZATIONAL UNIT (OU) STRUCTURE
45 # -----------------------------------------------------------------------------------------------------------------
46 # Define the organizational hierarchy for account management and policy inheritance
47 #
48 # STRUCTURE:
49 # /root - Top-level organization (all policies here apply to entire org)
50 # ├── /root/core - Core infrastructure accounts (network, security, log archive)
51 # ├── /root/sandbox - Experimental/testing accounts with relaxed policies
52 # ├── /root/suspended - Disabled accounts (all access blocked except org admin)
53 # ├── /root/transitional - Accounts being migrated or decommissioned
54 # └── /root/workloads - Production and non-production workload accounts
55 # ├── /root/workloads/prod - Production workloads (strictest policies)
56 # ├── /root/workloads/dev - Development workloads
57 # └── /root/workloads/test - Testing workloads
58 #
59 # BEST PRACTICES:
60 # - Use nested OUs to inherit policies from parent OUs
61 # - Separate production from non-production for different security postures
62 # - Keep sandbox isolated for experimentation without affecting production
63 # - Use suspended/transitional OUs for security incidents or account lifecycle management
64 # -----------------------------------------------------------------------------------------------------------------
65 organizational_unit_paths = [
66 "/root/core",
67 "/root/sandbox",
68 "/root/suspended",
69 "/root/transitional",
70 "/root/workloads",
71 "/root/workloads/prod",
72 "/root/workloads/dev",
73 "/root/workloads/test"
74 ]
75
76 # -----------------------------------------------------------------------------------------------------------------
77 # ORGANIZATION POLICIES - SECURITY GUARDRAILS
78 # -----------------------------------------------------------------------------------------------------------------
79 # This section applies Service Control Policies (SCPs), Resource Control Policies (RCPs), and other policies
80 # to enforce security, compliance, and operational guardrails across your organization.
81 #
82 # POLICY TYPES:
83 # - SERVICE_CONTROL_POLICY: Define maximum permissions for IAM principals (never grants, only restricts)
84 # - RESOURCE_CONTROL_POLICY: Define maximum permissions for resources (what can be done TO a resource)
85 # - BACKUP_POLICY: Configure automated backup plans for AWS Backup
86 #
87 # POLICY APPLICATION:
88 # Policies are applied in order and inherited down the OU hierarchy. Multiple policies combine with
89 # logical AND - all applicable policies must allow an action for it to succeed.
90 #
91 # CONFIGURATION APPROACH:
92 # 1. Start with baseline security (enabled below)
93 # 2. Gradually add stricter controls as needed
94 # 3. Test with dedicated accounts before applying to production
95 # 4. Use commented alternatives for future hardening
96 # -----------------------------------------------------------------------------------------------------------------
97 organization_policies = [
98 # EXAMPLE: Custom SCP (commented out - use for organization-specific policies)
99 # You can define inline SCPs here if you have custom requirements not covered by guardrail templates
100 # {
101 # policy_name = "scp_deny_all_outside_eu_regions"
102 # policy_type = "SERVICE_CONTROL_POLICY"
103 # target_ou_paths = ["/root/workloads"]
104 # target_account_ids = []
105 # policy_json = "INSERT_SCP_JSON"
106 # }
107
108 # ---------------------------------------------------------------------------------------------------------
109 # BASELINE SERVICE CONTROL POLICIES (SCPs)
110 # ---------------------------------------------------------------------------------------------------------
111 # These policies are defined in 'ntc_organizations_guardrails.tf' and provide foundational security controls
112 # See that file for detailed documentation on each policy's purpose and configuration
113 # ---------------------------------------------------------------------------------------------------------
114
115 # SCP 1: Organization-wide Security Baseline
116 # Prevents accounts from leaving org, blocks root user actions, denies IAM user creation
117 # Applied to: /root (entire organization)
118 module.ntc_guardrail_templates.service_control_policies["scp_root_ou"],
119
120 # SCP 2: Suspended/Transitional Account Lockdown
121 # Blocks all AWS service access for suspended or transitional accounts
122 # Applied to: /root/suspended, /root/transitional
123 module.ntc_guardrail_templates.service_control_policies["scp_suspended_ou"],
124 ]
125
126 # -------------------------------------------------------------------------------------------------------------------
127 # CLOUDTRAIL ORGANIZATION TRAIL - CENTRALIZED AUDIT LOGGING
128 # -------------------------------------------------------------------------------------------------------------------
129 # Create an organization-wide CloudTrail that logs API activity across ALL accounts
130 #
131 # PREREQUISITES:
132 # ⚠️ S3 log archive bucket MUST be provisioned BEFORE creating the organization trail
133 # ⚠️ KMS key for CloudTrail encryption must exist and have proper key policy
134 #
135 # WHAT THIS LOGS:
136 # - All AWS API calls across all accounts in the organization
137 # - Management events (control plane operations like creating EC2 instances)
138 # - Optional: Data events (data plane operations like S3 object access)
139 #
140 # SECURITY & COMPLIANCE:
141 # ✓ Required for SOC 2, ISO 27001, PCI DSS compliance
142 # ✓ Critical for incident response and forensics
143 # ✓ Enables detective controls for security threats
144 # ✓ Immutable audit trail (when S3 bucket has proper policies)
145 #
146 # CLOUDWATCH INTEGRATION:
147 # - Enables real-time monitoring and alerting
148 # - Allows metric filters for specific API calls
149 # - Powers CloudWatch Alarms for security events
150 # - Small additional cost but provides immediate visibility
151 # -------------------------------------------------------------------------------------------------------------------
152 organization_trail = {
153 kms_key_arn = local.ntc_parameters["log-archive"]["log_bucket_kms_key_arns"]["org_cloudtrail"]
154 s3_bucket_name = local.ntc_parameters["log-archive"]["log_bucket_ids"]["org_cloudtrail"]
155
156 # Enable real-time CloudWatch Logs for immediate visibility and alerting
157 cloud_watch_logs_enable = false
158 cloud_watch_logs_retention_in_days = 30
159 # cloud_watch_logs_existing = false # Set to true if log group already exists
160 # cloud_watch_logs_group_name = "organization-trail-logs" # Customize log group name
161 # cloud_watch_logs_role_name = "organization-trail-logs" # Customize IAM role name
162 }
163
164 # -------------------------------------------------------------------------------------------------------------------
165 # CENTRALIZED ROOT ACCESS MANAGEMENT
166 # -------------------------------------------------------------------------------------------------------------------
167 # NEW FEATURE: Manage root user credentials from the management account (available late 2024)
168 #
169 # SECURITY BENEFITS:
170 # ✓ Eliminates risk of forgotten root credentials in member accounts
171 # ✓ Prevents unauthorized root access in individual accounts
172 # ✓ Enables centralized audit of all root user activities
173 # ✓ Simplifies root credential management across hundreds of accounts
174 # ✓ New accounts created have NO root credentials by default
175 #
176 # FEATURES:
177 # 1. RootCredentialsManagement:
178 # - Delete root user passwords from member accounts
179 # - Audit root credential usage across organization
180 # - Enable password recovery for specific accounts when needed (break-glass)
181 # - Root credentials managed only from management account
182 #
183 # 2. RootSessions:
184 # - Perform privileged root actions from management account
185 # - Break-glass access for emergency situations:
186 # * Delete misconfigured resource policies (S3, SQS, KMS)
187 # * Fix broken IAM policies blocking all access
188 # * Recover from lockout situations
189 # - All actions logged in CloudTrail for audit
190 #
191 # Reference: https://docs.aws.amazon.com/IAM/latest/UserGuide/id_root-enable-root-access.html
192 # -------------------------------------------------------------------------------------------------------------------
193 centralize_root_access = {
194 enabled = true
195 features = [
196 "RootCredentialsManagement", # Centrally manage root credentials (delete, audit, recovery)
197 "RootSessions", # Perform emergency root actions from management account
198 ]
199 }
200
201 # -------------------------------------------------------------------------------------------------------------------
202 # DELEGATED ADMINISTRATORS - SERVICE DELEGATION
203 # -------------------------------------------------------------------------------------------------------------------
204 # Delegate administration of specific AWS services to designated accounts (typically Security, Backup, or Network)
205 #
206 # PREREQUISITES:
207 # ⚠️ Service must be enabled in 'service_access_principals' above (enables trusted access with Organizations)
208 # ⚠️ Delegated administrator account must already exist in the organization
209 # ⚠️ Delegated admin must be a MEMBER account (cannot use management account)
210 #
211 # WHY DELEGATE:
212 # ✓ Centralized management from specialized accounts (security, backup, networking)
213 # ✓ Separation of duties: Management account for org structure, specialized accounts for their domains
214 # ✓ Reduced risk: Limits blast radius if management account is compromised
215 # ✓ Best practice: AWS recommends minimal usage of management account
216 #
217 # DELEGATION TYPES:
218 #
219 # GLOBAL DELEGATION (once per organization):
220 # Services delegated organization-wide, not per region:
221 # - AWS Config: Centrally manage compliance rules across organization
222 # - IAM Access Analyzer: Analyze resource policies organization-wide
223 # - AWS Backup: Centralized backup management and policies
224 # - CloudFormation StackSets: Cross-account deployments
225 # - Organizations, SSO/Identity Center, etc.
226 #
227 # REGIONAL DELEGATION (per region):
228 # Services requiring delegation in EACH region you operate:
229 # - Security Hub: Aggregate security findings per region
230 # - GuardDuty: Threat detection per region
231 # - Inspector: Vulnerability scanning per region
232 # - Macie: Sensitive data discovery per region
233 # - Audit Manager: Compliance auditing per region
234 # - IPAM: IP address management per region (optional - can also run centralized without delegation)
235 #
236 # DELEGATION PROCESS:
237 # 1. Service must be enabled in Organizations (via service_access_principals)
238 # 2. Delegated admin account receives permissions to manage service org-wide/regionally
239 # 3. Member accounts are automatically enrolled/managed by delegated admin
240 #
241 # COMMON PATTERNS:
242 # - Security services → Security account (creates centralized SOC)
243 # - Backup → Backup/Log Archive account (centralized backup management)
244 # - IPAM → Network account (centralized IP address management)
245 # -------------------------------------------------------------------------------------------------------------------
246 delegated_administrators = [
247 {
248 service_principal = "guardduty.amazonaws.com"
249 admin_account_id = local.security_account_id
250 regions = [
251 "eusc-de-east-1", # Brandenburg
252 ]
253 },
254 {
255 service_principal = "config.amazonaws.com"
256 admin_account_id = local.security_account_id
257 regions = [
258 "eusc-de-east-1", # Brandenburg
259 ]
260 },
261 ]
262}Want to dive deeper into the technical details?
Why Organizations Choose NTC
Trusted by government agencies and regulated enterprises
Up to 90% Faster
What takes 6-12 months from scratch takes 2-4 weeks with NTC. Deploy the full platform blueprint and start building your applications immediately.
Secure by Default
Every module follows AWS security best practices. Built-in guardrails, SCPs, and security controls prevent misconfigurations before they happen.
Full Control
NTC is deployed in your environment and you have full control of what is deployed and how. You get updates and support as long as you have a valid subscription.
GitOps Native
Designed for CI/CD from day one. Works seamlessly with Terraform Cloud, Spacelift, GitHub Actions, and your existing DevOps workflows.
Enterprise-grade
Trusted by government agencies and regulated industries. Proven in real-world production environments with hundreds of applications.
Modular & Flexible
Use what you need. Each module is independently versioned and can be composed to match your exact requirements and architecture.
Nuvibit: Sovereignty Experts
As an AWS Advanced Partner with the AWS Government Competency, Nuvibit specializes in building sovereign cloud platforms for regulated industries.
Need Implementation Support?
Get expert help deploying your applications, modernizing workloads, and migrating to AWS ESC through our certified system integrator partners.

adesso SE
Certified AWS partner specializing in application modernization, cloud migration, and sovereign cloud implementations. adesso combines deep technical expertise with proven methodologies to help you deploy and optimize workloads on the NTC platform.
Learn More About Partnership
tecRacer
AWS Premier Partner with deep expertise in cloud migrations, managed services, and infrastructure automation. tecRacer helps organizations accelerate their journey to the AWS European Sovereign Cloud with proven delivery methodologies and hands-on engineering teams.
Learn More About PartnershipStart Your AWS ESC Journey Today
Let's discuss the next steps to accelerate your sovereign cloud journey.

